Hitting the Gym: The Anatomy of a Killer Workout (TROOPERS 2019)
On March 18th 2019 myself and Dimitrios Valsamaras delivered a presentation on cybersecurity vulnerabilities of "smart" fitness equipment, entitled "Hitting the Gym: The Anatomy of a Killer Workout" at the TROOPERS 2019 conference (NGI track).
The presentation started with an overview of the technology stack in modern fitness equipment. These devices can be characterized as IoT equipment (or "smart" devices), since they are IP-enabled and provide a plethora of Internet-based services to users (e.g. fitness tracking, social network interactions, video streaming etc.). By providing these auxiliary functionalities, the device vendors have increased the information security attack surface of these devices.
Normally, for devices that come into contact with human operators and where there is an increased risk of a fatal or near-fatal accident, there are certain pre-market and post-market requirements that must be met. For example, "smart" medical device vendors must take into consideration cybersecurity aspects during engineering and deployment. However, our study has found that up to now, "smart" fitness equipment have been exempted (or could be made to be exempted) from such controls both in the USA and in the EU.
To allow for such devices to be profitable, vendors often build upon an existing software stack or software ecosystem, that will provide them with both the required features (e.g. internet connectivity, UI controls, software package management, video player etc.) and security controls. We have found that many of these devices are built on top of the Android operating system, with some vendor contributed software to allow for hardware control. Sometimes though, this vendor contributed code may circumvent Android's security controls in order to achieve its purpose. Similarly, the vendor contributed code may also introduce its own security vulnerabilities to the device software stack.
Our study on "smart" fitness equipment began with a set of equipment spotted on the grounds of one of our customers during a Red Team type of security assessment. A set of vulnerabilities found in these devices allowed us to execute code on the devices, escalate privileges and remotely control their hardware. For example, in the case of a treadmill it was possible to modify remotely the speed and incline of the device. Such changes in configuration may result into a fatal accident.
With these devices entering the networks of military bases, universities, hotels and corporations they become an interesting entry point for attackers, which may be used to pivot to other systems. In fact, in our Red Team assessment, exploitation of such a device enabled us to enter a corporate Wi-Fi network.
One must also bear in mind that these devices are typically shared by users and are sometimes installed in areas that allow public/free access. Hence, it is possible for an attacker to conduct a so called "evil maid" attack, where he "tampers" (locally exploits a vulnerability and gains control of) a device and then retains remote control of the device while the next operators make use of the equipment. Another possible attack scenario is that of luring a victim operator into downloading malware from the World Wide Web. Although in the time we had available we did not identify a bug that could directly be exploited over the network, it is possible that such bugs may exist.
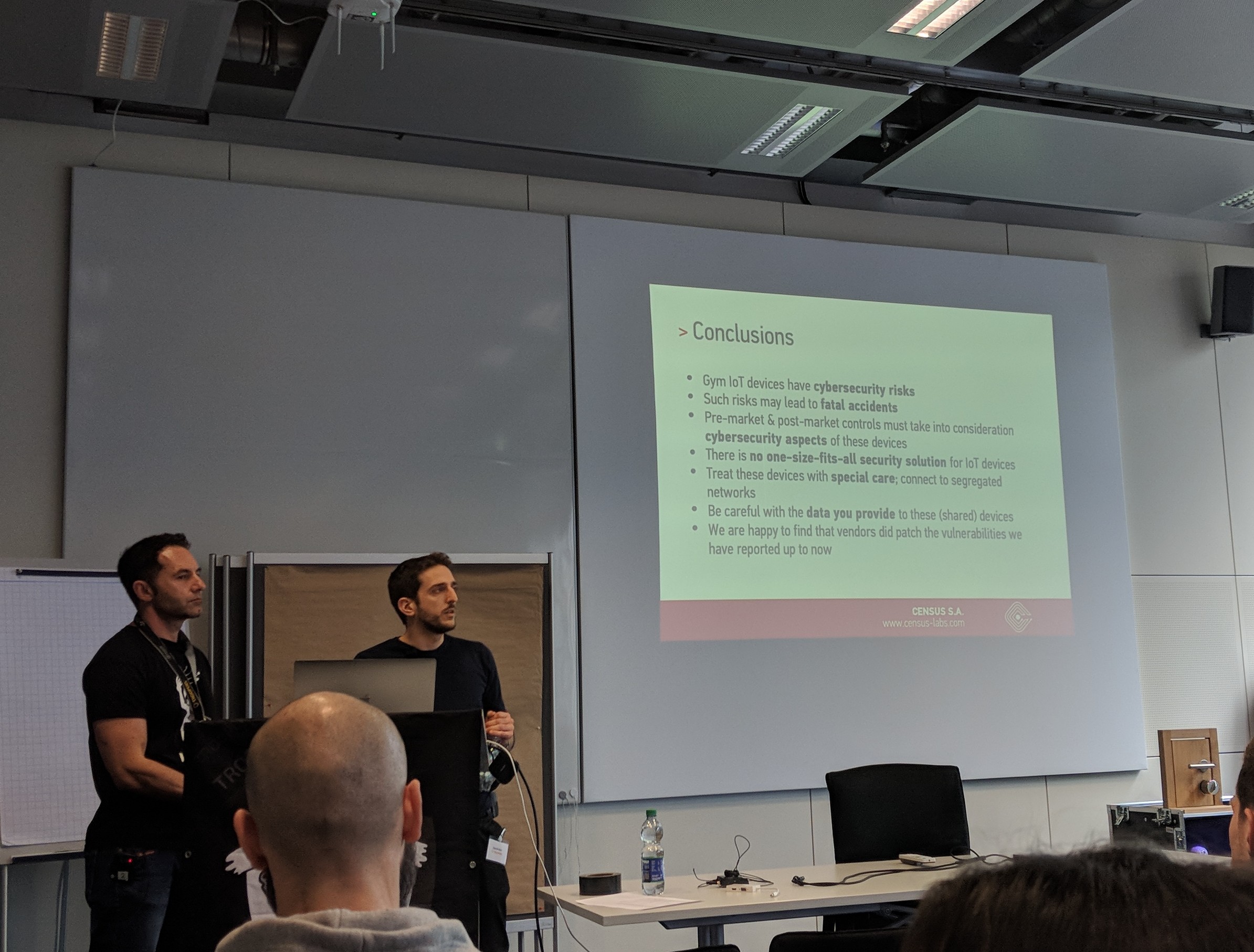
To summarize our conclusions:
- Gym IoT devices have cybersecurity risks
- Such risks may lead to fatal accidents
- Pre-market & post-market controls must take into consideration cybersecurity aspects of these devices
- There is no one-size-fits-all security solution for IoT devices
- Treat these devices with special care; connect to segregated networks
- Be careful with the data you provide to these (shared) devices
- We are happy to find that vendors are patching the vulnerabilities we have reported up to now
To raise awareness regarding the impact of our findings and the lack of cybersecurity pre-market / post-market controls in "smart" fitness equipment, the presentation was also delivered to the Medical Device and IoT groups of the European Union Agency for Network and Information Security (ENISA).
The related presentation material can be found below:
We would like to thank the TROOPERS 2019 organizers for an amazing event and hope to see everyone again next year!
