Lure10: Exploiting Windows Automatic Association Algorithm
Lure10 is a novel technique presented at the Hack-in-the-Box 2017 conference in Amsterdam that enables an attacker to automatically achieve a man-in-the-middle position against wireless devices running the Windows operating system. The attack requires no user interaction and exploits the "Wi-Fi Sense" feature found in recent versions of the Microsoft Windows platform.
Microsoft was informed about the issue and decided to disable the "Wi-Fi Sense" feature by default in Windows 10 version 1703.
If you are a Windows 10 or Windows Phone user, you can make sure that you are protected from this attack by disabling the Wi-Fi Sense feature: Open "Settings" → "Network & Internet" → "Wi-Fi" and turn off the "Connect to Suggested Open Hotspots".
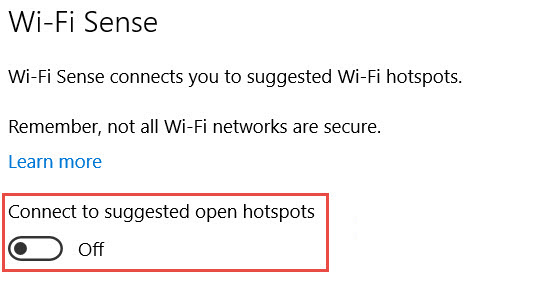
Figure 1: Disabling Wi-Fi Sense
Technical Details
Wi-Fi automatic association attacks allow attackers to force wireless clients to connect to an attacker-controlled Access Point, without requiring any user interaction. Once the association has been made, an attacker may then proceed to a man-in-the-middle attack to the unsuspecting victims. Many desktop and mobile applications still carry no proactive protections for man-in-the-middle attacks, thus allowing attackers to eavesdrop on (or even modify) the user's traffic.
The most popular automatic association technique is KARMA. This technique exploits the fact that wireless stations perform active scanning for networks they have associated with in the past. By capturing information from these probing frames, attackers may create a Rogue Access Point that mimics one of the searched-for (but public access) networks. This used to be all that was needed to get a wireless client to automatically connect to the attacker-controlled node. However modern devices mitigate this attack by either probing to the broadcast address with no ESSID leak, or by waiting to receive the right beacon frame from nearby networks.
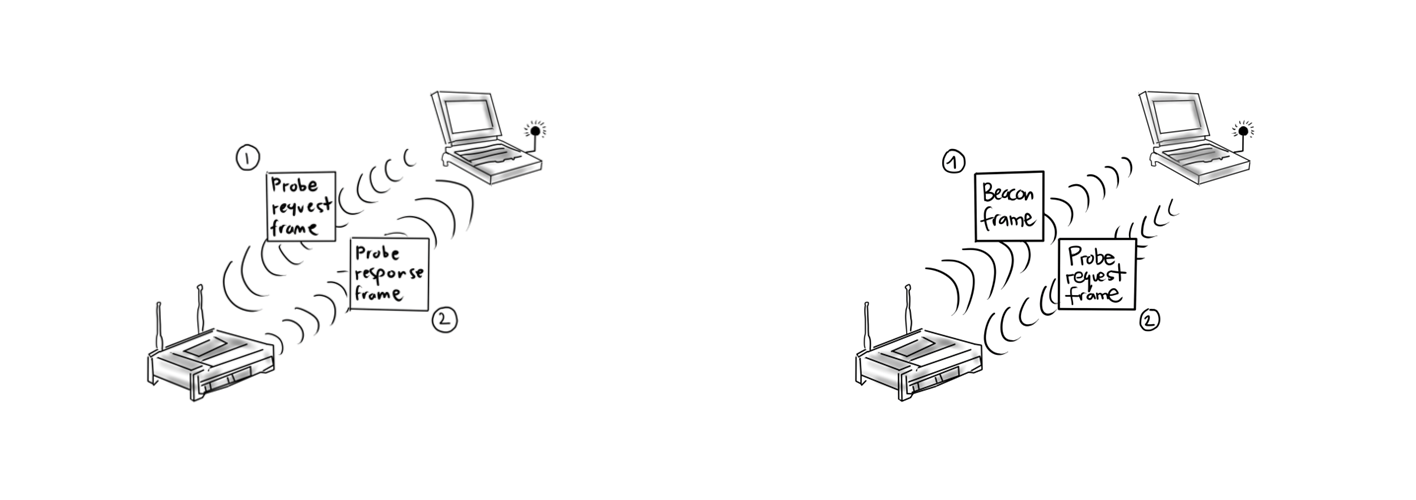
Figure 2: Old vs new probing behavior for known networks
This change has significantly hampered the usefulness of the KARMA attack. Windows took it a step further. Unless explicitly demanded, Windows will not add any open WLANs to the Preferred Network List (PNL) and hence, will not automatically send probe request frames for these networks.
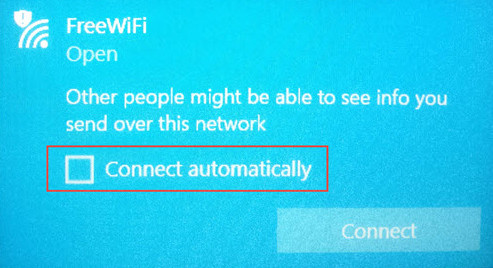
Figure 3: Open Wi-Fi networks are by default excluded from the Preferred Network List
While that means that the latest version of Windows is immune to the KARMA attack, automatic association on Windows became possible again through a different vector. Windows 10 were released with a new feature called Wi-Fi Sense. According to this feature's description:
At its time of release Wi-Fi Sense became a controversial topic as it allowed users to share Wi-Fi networks with their contacts and to be automatically connected to networks shared by their contacts. Microsoft removed this specific feature in Windows Build 14342. However, Wi-Fi Sense was not completely removed. By default Windows hosts would continue to automatically connect to Wi-Fi Sense networks.
So how is a network tagged as Wi-Fi Sense? When Windows hosts connect to open networks they send information back to Microsoft about its quality. Microsoft collects this information and builds a database of high-quality open networks, that are tagged as Wi-Fi Sense networks. Microsoft seems to store the ESSID and the geolocation data of each of these networks.
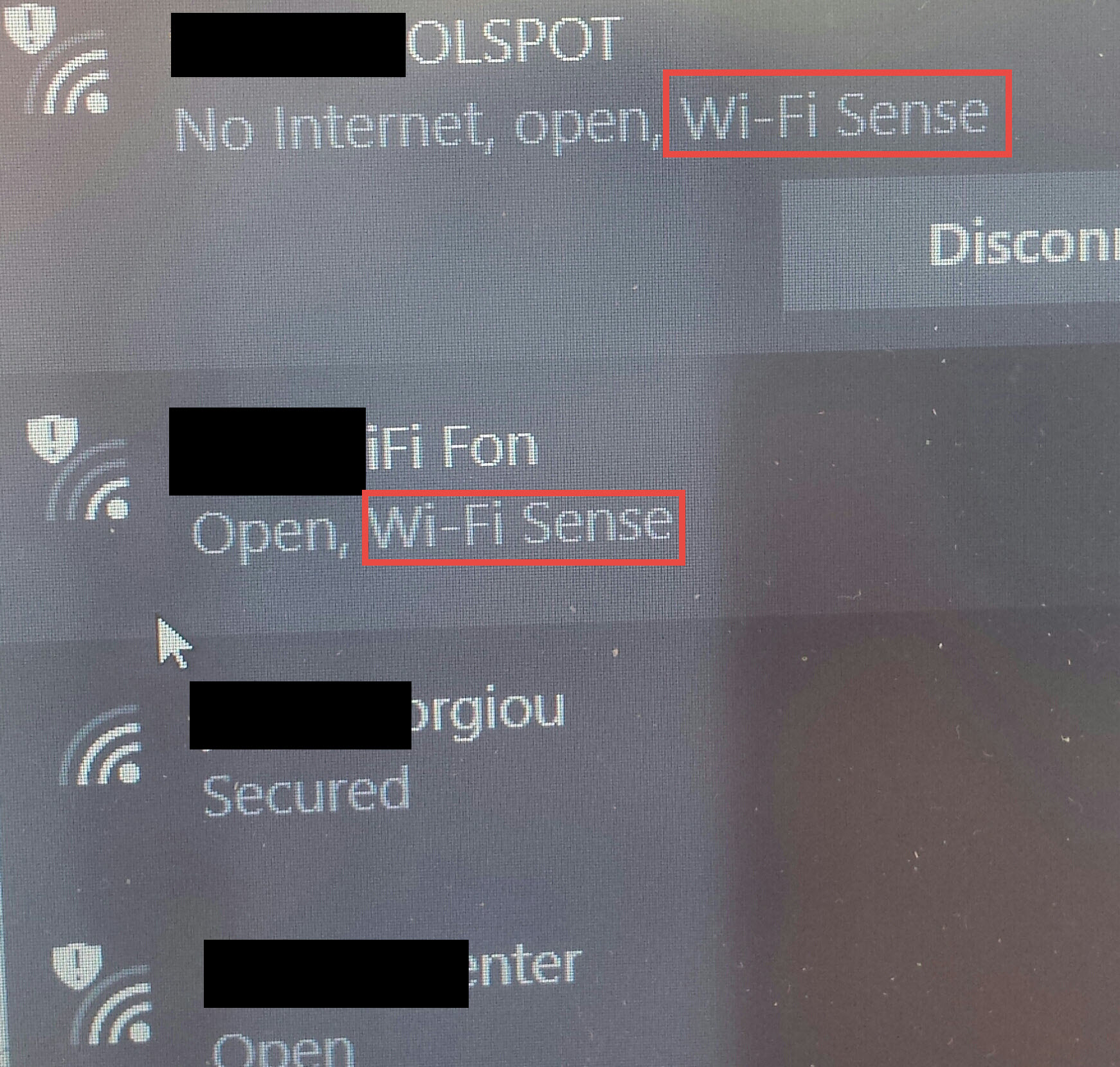
Figure 4: Wi-Fi Sense tagged networks
Microsoft will push to Windows devices a Wi-Fi Sense Network List (SNL) with high-quality networks. We noticed that not all Windows devices share the same Wi-Fi Sense WLANs in their SNL. For example, we noticed that a device that successfully identified Wi-Fi Sense WLANs in Athens, failed to identify any in San Francisco. It seems that Microsoft pushes Wi-Fi Sense networks that are within a certain distance from the user's "common location".
Fooling Windows Location Service
In order to exploit Wi-Fi Sense and cause an automatic association, one needs to first trick the victim's device into believing it is within the geographical area of a Wi-Fi Sense tagged WLAN and then mimic that Wi-Fi Sense WLAN.
Behind the Windows Location Service mechanism lies a Wi-Fi Positioning System (WPS). Windows hosts send the BSSIDs (MAC addresses) of nearby Access Points to Microsoft’s WPS. The WPS queries a database that correlates location data with Access Point BSSIDs and returns the location of the host.
It appears that Microsoft's WPS only cares for the BSSIDs of nearby WLANs. An attacker that crafts and broadcasts beacon frames carrying BSSIDs from a certain area will make the Windows Location Service (of a nearby Windows device) believe it is within that area. It's worth mentioning that all apps and services that rely on Windows Location Service as a security control are vulnerable to this threat.
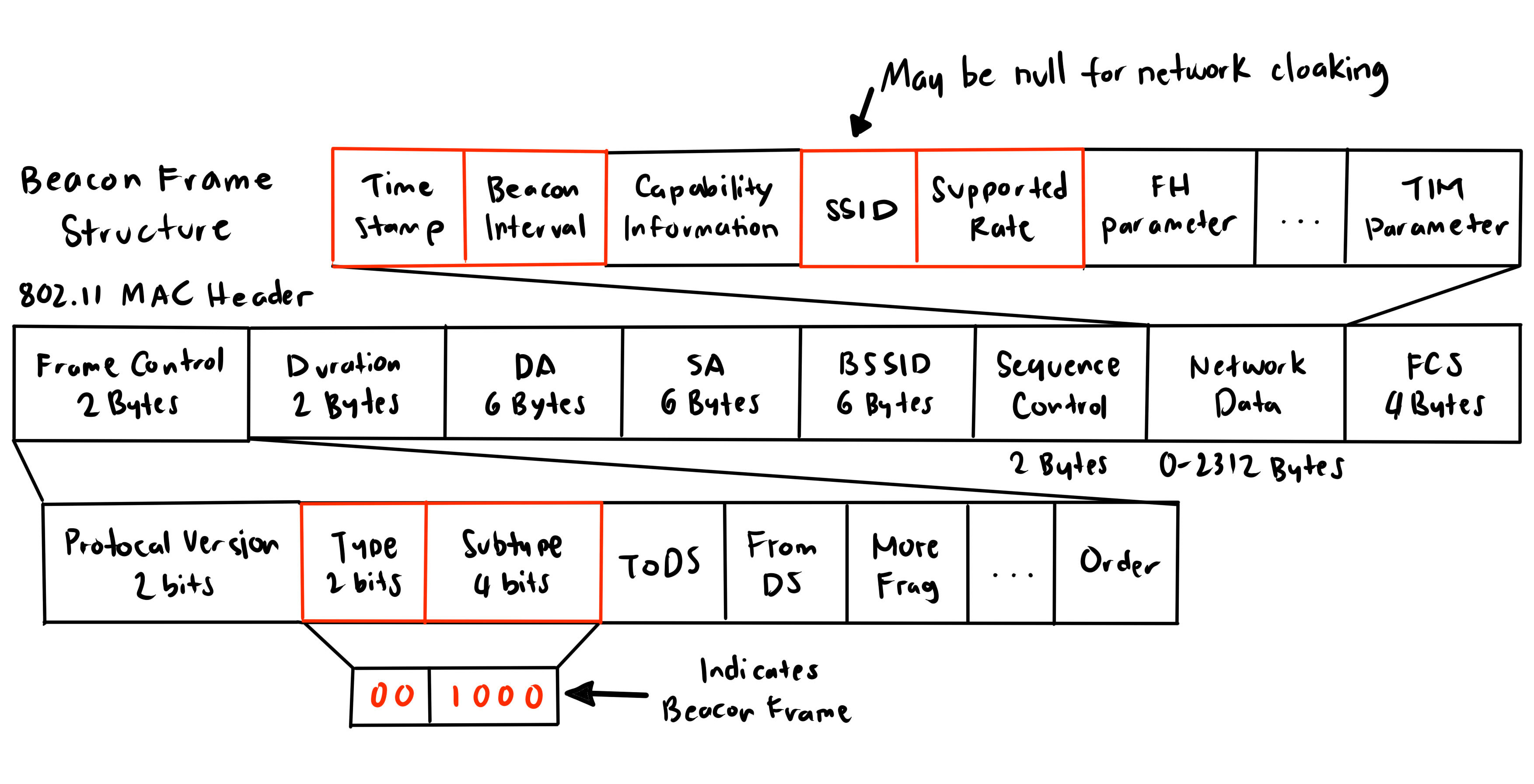
Figure 5: Beacon frame structure
Since Microsoft WPS only cares for BSSIDs, the beacon frames may have a null ESSID (network cloaking) to reduce suspicion (networks with a null ESSID don't appear in the list of nearby Wi-Fi networks).
Exploiting Windows Automatic Wireless Association Algorithm
To perform the attack, we need to spot a Wi-Fi Sense WLAN that exists in the victim's SNL. Good candidates for this are Wi-Fi Sense WLANs that are in the same area (e.g. city) as the victim.
If there is an increased number of Wi-Fi neighbor networks around the Wi-Fi Sense network, it will allow for easier forging of the network location. WiGLE can help identify areas with multiple Wi-Fi networks.
To the best of our knowledge Microsoft provides no public API for the geolocation of Wi-Fi Sense tagged WLANs. Hence to locate one, wardriving is the way to go.
Networks that are likely to be tagged as Wi-Fi Sense are public hotspots in airports, or cafe's. Hotspots that belong to Fon (or similar) networks, where users share part of their bandwidth, so that they could connect to other members' hotspots, are also likely to become tagged as Wi-Fi Sense.
Once an appropriate Wi-Fi Sense WLAN has been identified, the attacker needs to capture
- the BSSIDs of the Access Points (APs) in this area, and
- the ESSID of the Wi-Fi Sense tagged network
The attacker will then broadcast beacon frames with the above data, within the Wi-Fi range of a victim device running Windows 10 / Windows Phone 8.1 operating system. The Windows Location Service of the device will subsequently believe it is within the area of the above Wi-Fi Sense network.
For Windows devices that are already associated with a wireless network, the attacker will need to also mount a de-authentication attack. In this attack, deauthentication / disassociation frames are sent to the wireless access point with a spoofed source address, i.e. that of the victim Wi-Fi device.
The deauthentication attack will disrupt any existing associations leaving the victim device in the "network discovery" phase. During this phase, Windows will proceed with the automatic association algorithm, which runs as follows:
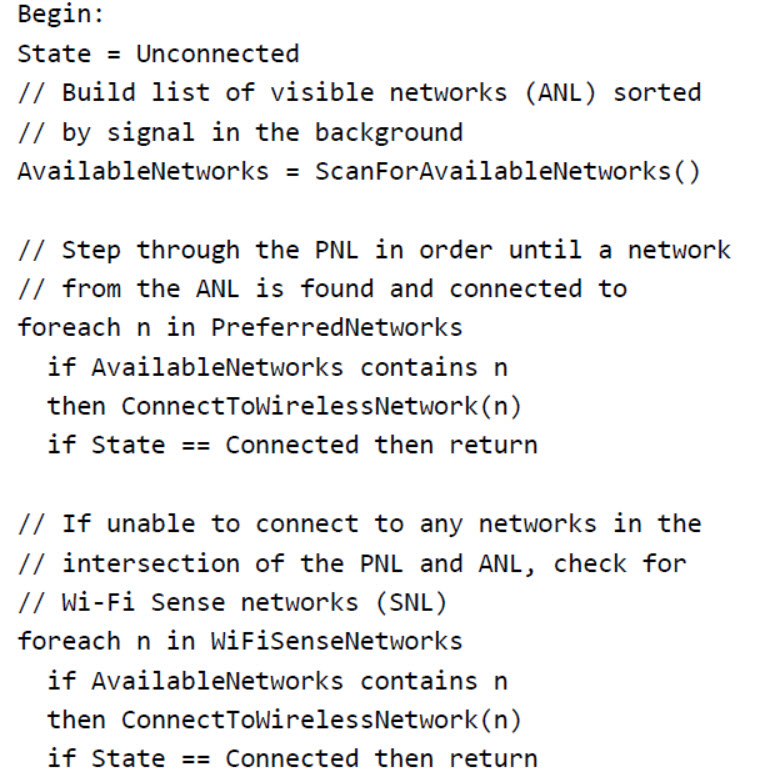
Figure 6: Windows Automatic Association Algorithm
According to this algorithm, there are two common cases:
Case 1: There are no networks in common in the PNL and ANL lists
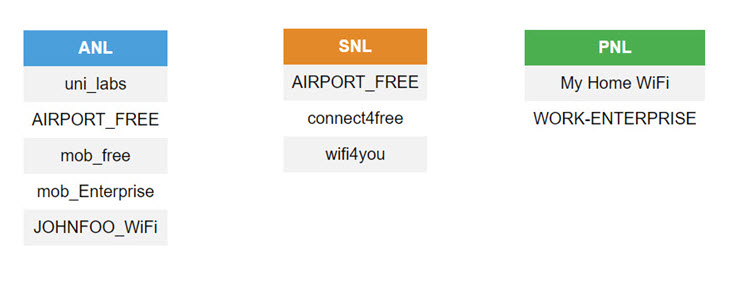
Figure 7: The PNL and ANL have no networks in common
In this scenario there are no networks around that the victim has connected to in the past (and added in the PNL). In this case, the victim device will automatically connect to the available (rogue) Wi-Fi Sense hotspot with ESSID "AIRPORT_FREE".
Case 2: There is at least one network in common in the PNL and ANL
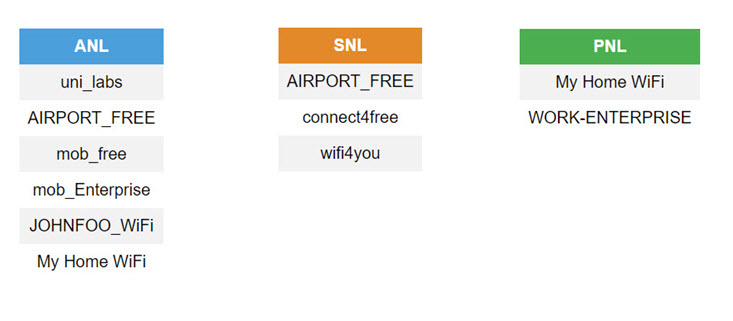
Figure 8: The "My Home WiFi" network is part of both the PNL and ANL
In this case, apart from our rogue Wi-Fi Sense network "AIRPORT_FREE", there is also a network that the victim has stored in its PNL (i.e. the victim has connected to this network in the past) named "My Home WiFi". In this case, the victim device will prefer to associate with the "My Home WiFi" WLAN, found in the PNL. However, it is possible to prevent this association by performing a jamming attack to the "My Home WiFi" network. Such a jamming attack can be performed using commodity hardware. Once jamming takes place the "My Home WiFi" Access Point will essentially "disappear" from the victim node's ANL, leading to a situation identical to that of Case 1.
Figure 9 summarizes the attack actions.
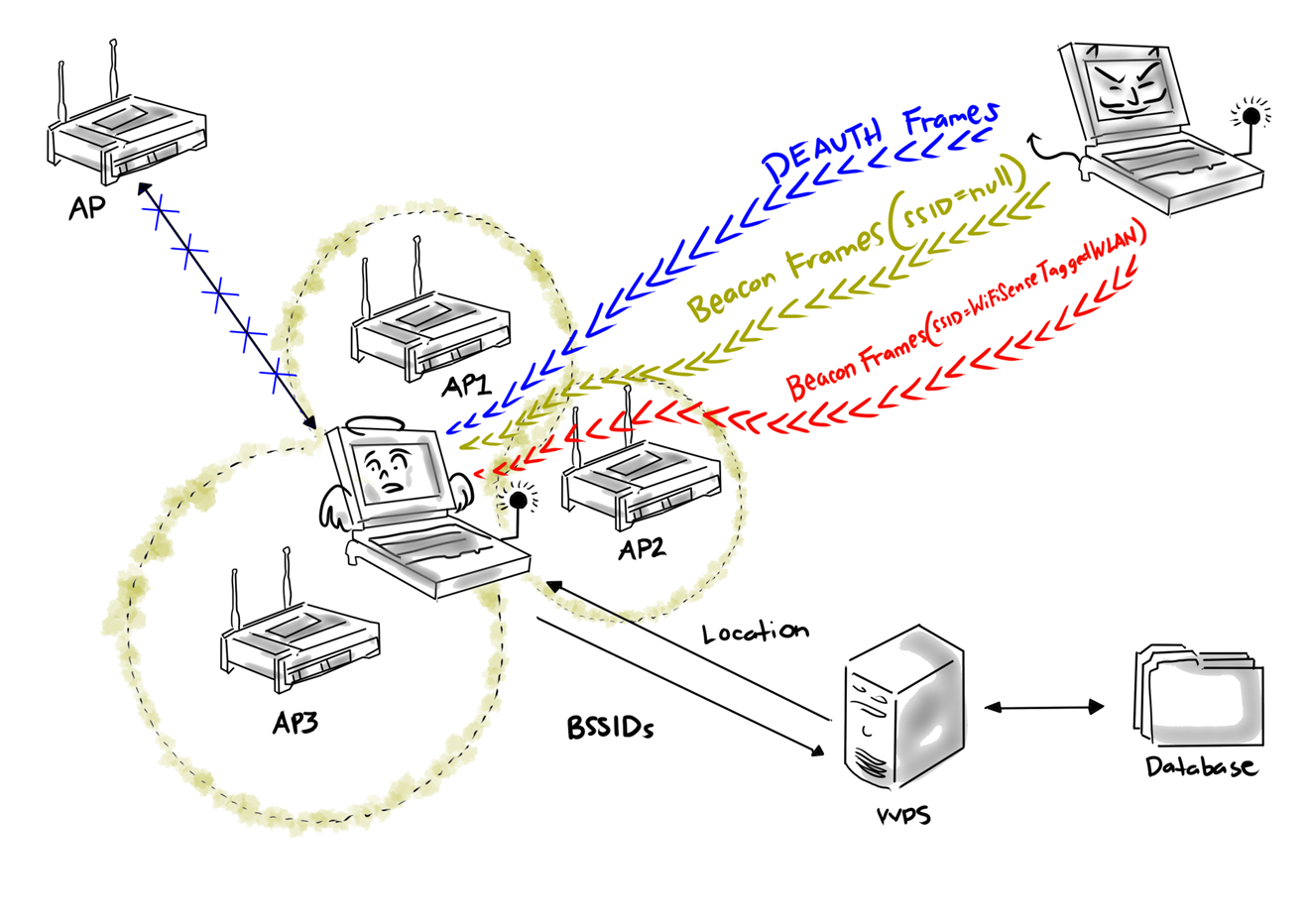
Figure 9: The Lure10 attack
Automating the attack with wifiphisher
Version 1.3 of the wifiphisher rogue Access Point tool comes with support for the Lure10 attack.
The following command collects all needed information from the area of the Wi-Fi Sense tagged WLAN:
root@kali:~# wifiphisher --lure10-capture --nojamming
Figure 10 shows the output of the above command.
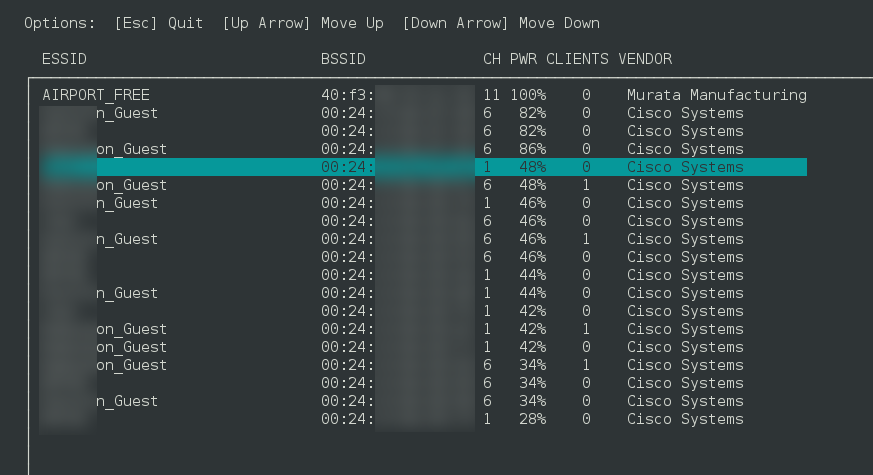
Figure 10: Capturing Access Point information from the area of the actual "AIRPORT_FREE" Wi-Fi Sense tagged network
The Wi-Fi area information is stored in file "area_20170415_032528". The "AIRPORT_FREE" Wi-Fi Sense tagged network can now be replicated in another area, as part of a man-in-the-middle attack, using the following command:
root@kali:~# wifiphisher --lure10-exploit area_20170415_032528 --essid "AIRPORT_FREE"
The video below shows a demonstration of the attack to a Windows host.
Issue Timeline
Microsoft is first contacted about this issue on September 5th, 2016. The issue is assigned an internal ID on September 6th, 2016. The vendor triage process states on September 27th, 2016 that "[the issue is] not unexpected and has been reviewed since WiFi Sense development. This is considered an accepted risk that the team has been aware of. There are no plans to release a patch at this time; the ability to fake the location is new but does not change their [i.e. the team's] stance on the issue."
On April 13th, 2017 the attack is presented at the COMMSEC track of the Hack in the Box 2017 Amsterdam conference. On April 15th, 2017 version 1.3 of the wifiphisher tool is released, that automates the attack. On April 25, 2017 Microsoft releases KB4016240 (OS Build 15063.250) of Windows 10 version 1703 that turns off Wi-Fi Sense by default on all new Windows installations. Furthermore, Microsoft removes the brand name "Wi-Fi Sense", and the feature is from then on referred to as "Connect to suggested open hotspots". Microsoft also updates the related privacy page.
Presentation Material
Material from the Hack in the Box 2017 Amsterdam presentation can be found below:
