Introducing wifiphisher - BSides London 2015
Hello. My name is George Chatzisofroniou (@_sophron) and I work as a security engineer at CENSUS. This summer I gave a talk at BSides London. The talk was called ‘Introducing wifiphisher, a tool for automated WiFi phishing attacks’ and revolved around the recently published tool.
Wifiphisher is a security tool that mounts phishing attacks against WiFi networks. I released it in early 2015 and since then it became quite popular with a lot of press coverage. Community-driven BSides London seemed to be the perfect choice for introducing the tool and clarifying its purpose.
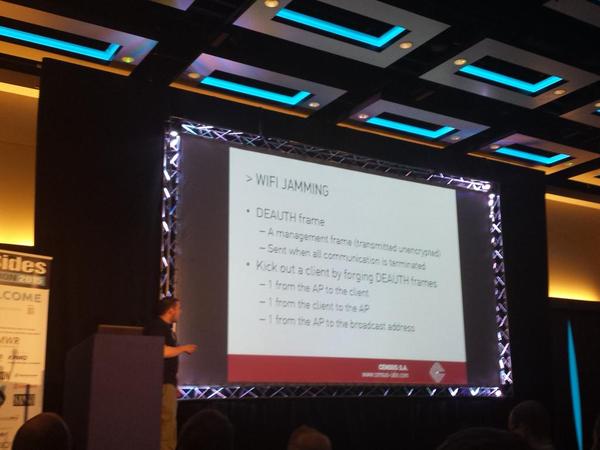
In the first part of my talk, I explained in detail Karma and Evil Twin — two WiFi man-in-the-middle attacks. Both of these attacks exploit the lack of encryption in management frames by forging DEAUTH packets and then disrupting any existing associations of the targeted network. Furthermore, both attacks take advantage of the auto-connect flag that is enabled by default in modern network managers by setting up a rogue Access Point that the victim will eventually connect to. In Karma, the phony Access Point is created based on probe request frames, whereas in the Evil Twin attack, the phony Access Point is modelled by the target Access Point. I showed how the success rates of these attacks differ depending on the environment and how differently network managers react to them.
In the second part, I introduced wifiphisher and showed how it automates the Evil Twin in order to mount phishing attacks. At that point, I compared wifiphisher with other similar tools (LINSET and Pineapple) and showed how one may contribute to the project.
Finally, I discussed common countermeasures against these attacks, including WIDPS, 802.11X and security awareness training.
Material from my talk can be found here:
- Presentation slides (pdf)
- Presentation video (youtube)
- Wifiphisher project page (github repo)
A related post about this talk was also published on Tripwire’s “State of Security” blog.
During the conference, I had a great time meeting new people and discussing interesting ideas regarding the future of the tool. Credit to the organisers of the event who made it real!
